Los ataques de phishing con IA en 2026 son más difíciles de detectar que nunca.
Ataques de phishing con IA en 2026 Ya no son intentos ruidosos y torpes de robar información, sino que se infiltran silenciosamente, casi indistinguibles de la comunicación cotidiana.
Anuncios
Hay algo ligeramente inquietante en la naturalidad con la que se sienten estos ataques.
Nada dramático, nada obviamente malintencionado; simplemente otro correo electrónico, otro mensaje, otra solicitud que encaja perfectamente en el ritmo de un día normal.
Es precisamente ahí donde se ha desplazado el riesgo.
Anuncios
Antes, la sospecha se desencadenaba por algo que parecía "extraño". Ahora, el peligro real a menudo parece completamente normal.
¡Sigue leyendo nuestro texto y aprende más!
Tabla de contenido
- ¿Qué son los ataques de phishing mediante IA y por qué son diferentes?
- ¿Cómo funcionan realmente los ataques de phishing mediante IA?
- ¿Por qué son? Ataques de phishing con IA en 2026 ¿Más difícil de detectar que nunca?
- ¿Qué hace que estos ataques sean psicológicamente efectivos?
- Ejemplos reales de ataques de phishing mediante IA
- Cómo protegerse de estas amenazas
- Diferencias clave: Ataques de phishing tradicionales frente a ataques de phishing basados en IA
- Preguntas frecuentes (FAQ)
Cuáles son Ataques de phishing con IA en 2026 ¿Y por qué son diferentes?
En apariencia, el phishing sigue persiguiendo el mismo objetivo: extraer información confidencial mediante el engaño.
Eso no ha cambiado. Lo que sí ha cambiado —de forma silenciosa pero decisiva— es lo creíble que se ha vuelto ese engaño.
Ataques de phishing con IA en 2026 Confía en sistemas capaces de generar un lenguaje que no solo parezca correcto, sino que además resulte familiar.
Los mensajes reflejan el tono, el ritmo e incluso los hábitos sutiles de comunicación. Esa familiaridad reduce las defensas antes de que surja la sospecha.
También se está produciendo un cambio más amplio en la forma en que se percibe la identidad en línea.
La comunicación se ha fragmentado: correos electrónicos, chats, notas de voz, confirmaciones rápidas. En ese entorno, la autenticidad suele darse por sentada en lugar de verificarse.
Estos ataques se aprovechan de esa suposición y se infiltran en rutinas que la gente rara vez cuestiona.
++ Toma de decisiones empresariales en mercados de alta volatilidad
¿Cómo lo hago? Ataques de phishing con IA en 2026 ¿Realmente funciona?
El proceso rara vez comienza con el mensaje en sí. Comienza con la observación.
Fragmentos de datos —publicaciones en redes sociales, perfiles públicos, interacciones pasadas— son suficientes para esbozar un perfil convincente de un objetivo.
A partir de ahí, las herramientas de IA generan mensajes que se ajustan a ese esquema. No son réplicas perfectas, pero sí lo suficientemente parecidas como para evitar fricciones.
El momento oportuno juega un papel sutil pero poderoso.
Poco después de realizar una compra en línea, aparece una notificación sobre la entrega. Durante una jornada laboral ajetreada, se recibe una solicitud de confirmación.
Estos momentos no son aleatorios; se eligen porque se ajustan a las expectativas existentes.
El phishing tradicional lanza una red amplia, con la esperanza de conseguir un gran volumen de usuarios.
Ataques de phishing con IA en 2026 Operamos más como una intrusión silenciosa, seleccionando objetivos con intención y abordándolos con contexto. Menos ruido, más precisión.
++ Los mercados digitales de franquicias están transformando las decisiones de compra en 2026.
¿Por qué son? Ataques de phishing con IA en 2026 ¿Más difícil de detectar que nunca?
El desafío no es solo tecnológico, sino también perceptivo.
Lenguaje utilizado para delatar estafas. Frases torpes, errores gramaticales, saludos genéricos.
Esas señales se están desvaneciendo. Los mensajes ahora se leen con fluidez, a veces incluso con un acabado más pulido que los auténticos.
Luego viene la superposición de capas. Un correo electrónico podría ir seguido de un mensaje de texto.
Un mensaje puede reforzarse con una llamada. Cada punto de contacto añade credibilidad, creando una sensación de continuidad difícil de cuestionar en tiempo real.
También existe una creciente superposición entre los estilos de comunicación personal y profesional. La informalidad se ha vuelto común, incluso en contextos empresariales.
Esa difuminación del tono elimina otra capa de defensa. Cuando todo parece informal, casi cualquier cosa puede pasar por legítima.
Un informe de seguridad de IBM de 2025 destacó que el phishing sigue estando implicado en aproximadamente un tercio de las filtraciones de datos a nivel mundial.
Esta persistencia no es casual; refleja la facilidad con la que el método se adapta a nuevos entornos.
++ Por qué la educación financiera se está convirtiendo en una habilidad de supervivencia.
¿Qué hace que estos ataques sean psicológicamente efectivos?
Existe la tendencia a tratar el phishing como un problema técnico, pero su fundamento es conductual.
La urgencia sigue siendo uno de los desencadenantes más eficaces.
Un mensaje que sugiere una acción inmediata —una alerta en la cuenta, un problema con un pago— acelera el proceso de toma de decisiones.
Bajo presión, la verificación se percibe como una demora que la gente no se puede permitir.
Sin embargo, la confianza es donde las cosas se vuelven más complejas. Cuando un mensaje refleja el tono de un colega o se asemeja a un patrón familiar, el escepticismo disminuye.
Ataques de phishing con IA en 2026 Aprovecha esta situación alineándote estrechamente con lo que el objetivo ya espera ver.
También existe el cansancio. La comunicación digital se ha vuelto constante, casi omnipresente. Las decisiones se toman rápidamente, a menudo sin mucha reflexión.
Los atacantes no necesitan ser más astutos que la víctima; solo necesitan un breve descuido, un momento en el que su atención se desvíe.
Así pues, la pregunta persiste: si algo se ajusta perfectamente a las expectativas, ¿qué motiva una segunda mirada?
Ejemplos reales de ataques de phishing mediante IA
Ejemplo 1: El correo electrónico familiar que pasó desapercibido
Un empleado del equipo de finanzas recibió lo que parecía ser una solicitud rutinaria de un gerente. El lenguaje coincidía con conversaciones anteriores.
El contexto hacía referencia a una tarea en curso. Nada destacaba.
Sin embargo, el archivo adjunto redirigía a una página de captura de credenciales. El acceso se vio comprometido en cuestión de minutos.
Lo que hizo que este caso fuera notable no fue la sofisticación técnica, sino lo común que pareció la interacción.
Ahí es a menudo donde Ataques de phishing con IA en 2026 Triunfar: no abrumando, sino mimetizándose.
Ejemplo 2: Una voz que sonaba demasiado real.
El dueño de una pequeña empresa recibió una llamada de alguien que sonaba exactamente como su contable.
La voz mantenía el mismo tono, el mismo ritmo, incluso con ligeras vacilaciones.
La solicitud implicaba una transferencia urgente debido a un supuesto problema bancario. El momento coincidía con la actividad financiera reciente. La decisión se tomó rápidamente.
Posteriormente, quedó claro que se había utilizado tecnología de clonación de voz.
Aquí es donde Ataques de phishing con IA en 2026 Ir más allá de la comunicación escrita, adentrándose en espacios donde la duda se siente casi antinatural.
Cómo protegerse de estas amenazas
Los hábitos defensivos están cambiando, aunque no siempre con la suficiente rapidez.
La verificación es cada vez menos opcional.
Cuando una solicitud implica información confidencial o transacciones financieras, la confirmación a través de un canal separado genera cierta fricción, pero una fricción útil. Interrumpe la narrativa del atacante.
La concienciación también importa, pero no en un sentido superficial.
Reconocer que la personalización en sí misma puede ser una táctica cambia la forma en que se interpretan los mensajes. La familiaridad ya no debe tomarse al pie de la letra.
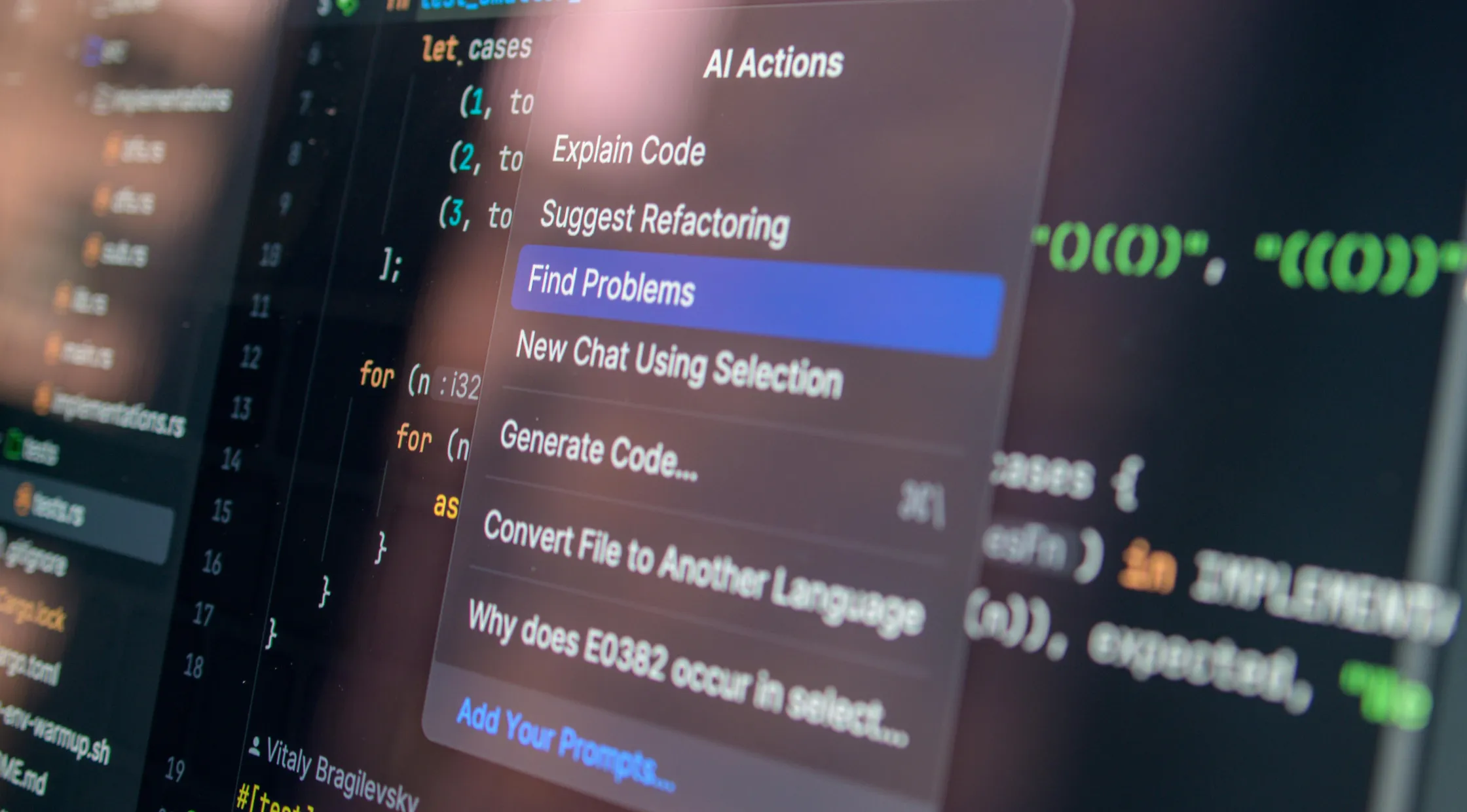
La tecnología sigue desempeñando un papel importante. Los filtros, los sistemas de autenticación y las herramientas de monitorización continúan mejorando.
Sin embargo, funcionan junto con el juicio humano, no en lugar de él. Y el juicio, bajo presión o fatiga, sigue siendo imperfecto.
Diferencias clave: Ataques de phishing tradicionales frente a ataques de phishing basados en IA
| Característica | Phishing tradicional | Ataques de phishing con IA en 2026 |
|---|---|---|
| Personalización | Mínimo | Altamente personalizado |
| Calidad del idioma | A menudo defectuoso | Natural y sensible al contexto |
| Objetivo | Amplio | Selectivo |
| Canales | Principalmente correo electrónico | Multicanal |
| Dificultad de detección | Manejable | Significativamente más alto |
| Enfoque psicológico | Básico | Sutil, basado en el comportamiento |
Preguntas frecuentes (FAQ)
| Pregunta | Respuesta |
|---|---|
| Cuáles son Ataques de phishing con IA en 2026? | Intentos avanzados de phishing que utilizan inteligencia artificial para crear mensajes altamente convincentes y personalizados. |
| ¿Son más peligrosas que el phishing tradicional? | En muchos casos, sí, debido a su realismo y enfoque específico. |
| ¿Realmente se puede utilizar la clonación de voz en estafas? | Sí, y ya se ha observado en escenarios de fraude financiero. |
| ¿Cuál es la protección más eficaz? | Verificación independiente y gestión cuidadosa de las solicitudes inesperadas. |
| ¿Corren mayor riesgo las personas o las empresas? | Ambos, especialmente aquellos que manejan información sensible o financiera. |
| ¿Siguen siendo útiles las herramientas de seguridad? | Sí, existen, pero no son suficientes sin la concienciación del usuario. |
Recursos recomendados
- Conozca las tendencias de phishing en el Informe de seguridad de IBM.
- Manténgase al día con la información sobre amenazas en ENISA.
Ataques de phishing con IA en 2026 están transformando el fraude digital de una manera que se percibe menos como una escalada y más como una integración.
No llaman la atención, sino que se integran, adaptándose a la forma en que la gente ya se comunica.
Ese es el cambio incómodo.
La amenaza ya no se define por el engaño evidente, sino por su capacidad de pasar desapercibida. Reconocer esa sutileza puede ser el primer paso real para resistirla.
